Britain’s health care system and much of Europe were back on track Saturday after a crippling worldwide cyber-extortion attack was stymied — purportedly all thanks to a cybersecurity researcher who bought a website for $10.69.
The researcher, who identifies himself online as MalwareTech, noticed that the malicious software that caused Friday afternoon’s attack consistently pinged an unregistered web domain. So he bought the website’s URL and made it live, he said.
That act essentially flipped a kill switch — halting the attack as it rippled worldwide, according to MalwareTech and the British government. By then, however, dozens of countries and some of their hospitals, companies and government offices were already infected.
“[Every] IP which hit the domain should have been stopped :),” MalwareTech told NBC News via email Saturday. He has declined to be identified in the media, but was described by the Guardian as a 22-year-old from southwest England who lives with his parents.
Still, researchers say, many computer systems continue to be infected by the “WannaCry” malware program and the domain fix may still leave some people, especially corporations, vulnerable.
“Many organizations, especially large corporations, use proxies and block direct Internet connections,” said Didier Stevens, a Belgian security researcher and handler at the Internet Storm Center who found that those who use proxy servers might still be affected.
Related: Cyberattack Hits Nearly 100 Countries With ‘Wanna Decryptor’ Malware
“It has stopped the attack for home users and small businesses that don’t use proxies,” Stevens told NBC News in an email, noting reports of new versions of the ransomware that are totally unaffected by the domain. “For organizations with proxies, other measures must be taken, like making sure anti-virus is working correctly and is up-to-date.”
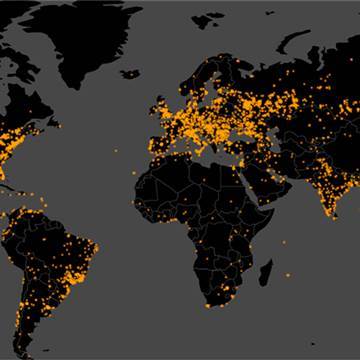
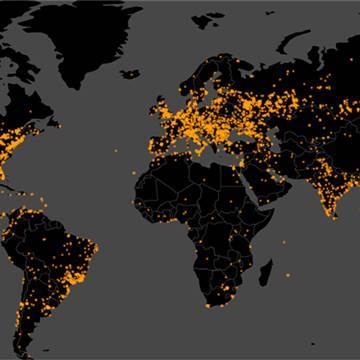
Nevertheless, MalwareTech’s purported accidental rescue of more than 100,000 computers in 104 countries was confirmed by the British government’s National Cyber Security Centre.

“Media reports today have rightly praised the efforts of MalwareTech to tackle the Wannacry cyber attack,” The National Cyber Security Centre said in a statement on Saturday. “The NCSC has been working in collaboration with a number of organisations in the cyber security community, including MalwareTech and 2SEC4, to understand and mitigate the current Wannacry ransomware threat.”
Avast, an antivirus provider, reported on Saturday that a total of 126,000 computers in 104 countries had been infected by the ransomware program — called “WanaCrypt0r 2.0.” or WannaCry. How it spread so quickly is unknown, although it’s believed to have been through email phishing.
“No confirmation of attack origin yet but a lot of people are saying spam,” MalwareTech explained, whose domain purchase provided him the identifying metadata of the affected computers.
But not everyone was saved from forking over money to the hackers’ ransom demands. According to Quartz, three accounts associated with the ransomware received 92 bitcoin payments, or about $26,408.
That the attack was potentially stymied is a relief to many, as the British government reported that U.K. hospitals were hit hard early during Friday’s cyberattack. Nearly all were operational again Saturday.
“In fact, 97 percent of the NHS trusts and hospitals and doctors are working as normal,” said British Interior Minister Amber Rudd after chairing the U.K. government’s crisis response team. “So the response has in fact been very good and that is due to the good work of the staff and the resilience that was already put in place.”
According to Rudd, 48 of 248 health service organizations went dark because of the cyberattack. Only six “have some limits on their business,” she added.
The cyberattack took control of any computer it infected and encrypted the information on it. It then demand a $300 payment to be made via Bitcoin in order for the user to regain access. More than 20 British hospitals and major institutions — including Nissan, FedEx, Russia’s Interior Ministry and German railway stations — were reportedly affected by the attack.
The identity of who was behind the malware was still unclear Saturday, but Europol’s European Cybercrime Centre said it was working with the impacted countries and with cybersecurity partners to defuse the situation and help victims.


Meanwhile, the Group of 7 (G7) countries — consisting of Canada, France, Germany, Italy, Japan, the United Kingdom and the United States — said they were not going to be caught flatfooted again. The G7’s financial chiefs met in Bari, Italy, on Saturday, ahead of the G7 Summit at the end of the month, and reportedly focused on the crisis.
“We recognize that cyber incidents represent a growing threat for our economies and that appropriate economy-wide policy responses are needed,” the G7 said in a statement.
Treasury Secretary Steven Mnuchin was in attendance and confirmed that cybersecurity would continue to be a main talking point for the…