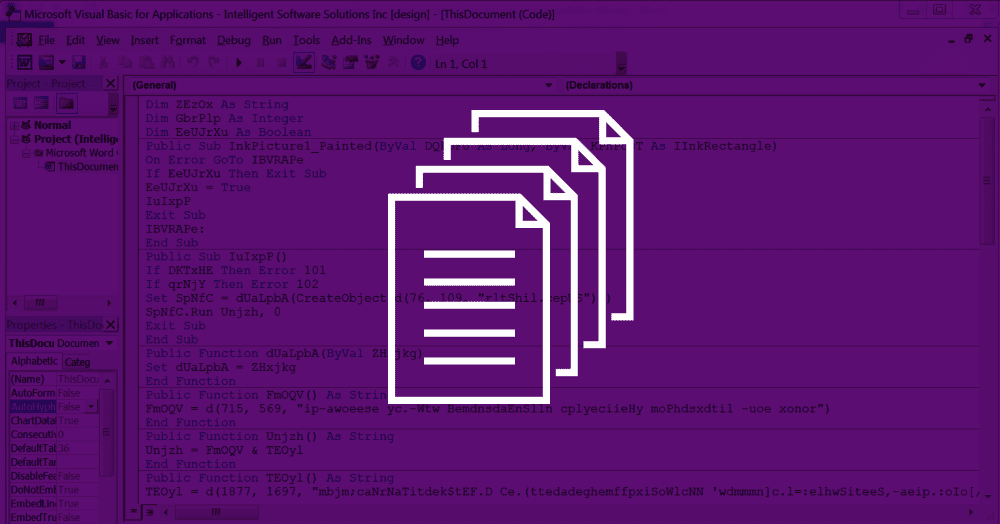
Recent versions of the Ursnif banking trojan have added a new series of tricks that allows the malware to detect when it’s being analyzed in a virtual machine or a sandbox environment.
These recent Ursnif samples have been seen recently, in the month of September, spread via macro-laced Office files attached to spam emails.
Before downloading and installing the malware, these macro scripts would perform a series of checks to determine if the PC they landed on is a real computer or a virtual machine or sandbox environment.
Proofpoint researchers identified four checks, of which, two were new, never seen before.
Checking files names for only decimal characters
The first new check was a lookup for unique characters in the names of local files. The macro script was specifically looking to see if local files contained only hexadecimal characters in their names.
Files submitted to analysis in sandbox environments and VMs are often renamed based on their SHA256 or MD5 hash, in order for researchers to keep track of the exact payload. SHA256 and MD5 hashes are only made up of the hexadecimal character set: 0123456789ABCDEFabcdef.
If the macro script found files with other types of characters, such as “w,” “=,” or “#,” then it knew this was a regular PC and not a researcher’s box, and go on with its installation procedure.
Second check looks for bloaty PCs
The second check is even more clever, with the macro script using the Application.Tasks.Count function to query the local OS for the presence of running processes with a graphical interface.
If the script found less than 50, the macro script would stop, thinking this was a test box for detecting malware.
“A quick check of a real system shows that it is common to have more than 50 tasks, while sandbox systems are optimized to have as few as possible,” the Proofpoint staff explained this check.
Former “new” anti-VM tricks become old anti-VM tricks
Besides these two new checks, the macro script also employed two checks that are relatively new but have been before. The macro script would first check for the presence of process names that included blacklisted terms, such as the names of VM vendors or reverse engineering software.
Then, the macro script would use the Maxmind API to detect the user’s IP address, and compare the IP to a list of known IP ranges assigned to security firms and data centers, where VMs and malware analysis toolkits are often hosted.
Anti-VM tricks trickles down from top-shelf banking trojans to low-level keyloggers
This last trick was seen before this past June, by both Proofpoint and Zscaler. Along with the Maxmind-powered query, the Proofpoint and Zscaler teams also detected macro scripts querying the local computer for the list of recently opened files.
If the number was less than three, the macro script would know this was a freshly installed VM, just for the purpose of analyzing malware and stop the installation process.
In June, Proofpoint detected the Dridex banking trojan employing these tricks (Recent Files check and Maxmind query), while Zscaler detected these two with the Matsnu backdoor trojan, the Nitol backdoor trojan, and the Nymaim ransomware.
These two checks appeared to have become standard practice now, with SentinelOne reporting in September that basic keyloggers were also using these anti-VM techniques.